Password vulnerability in cybersecurity
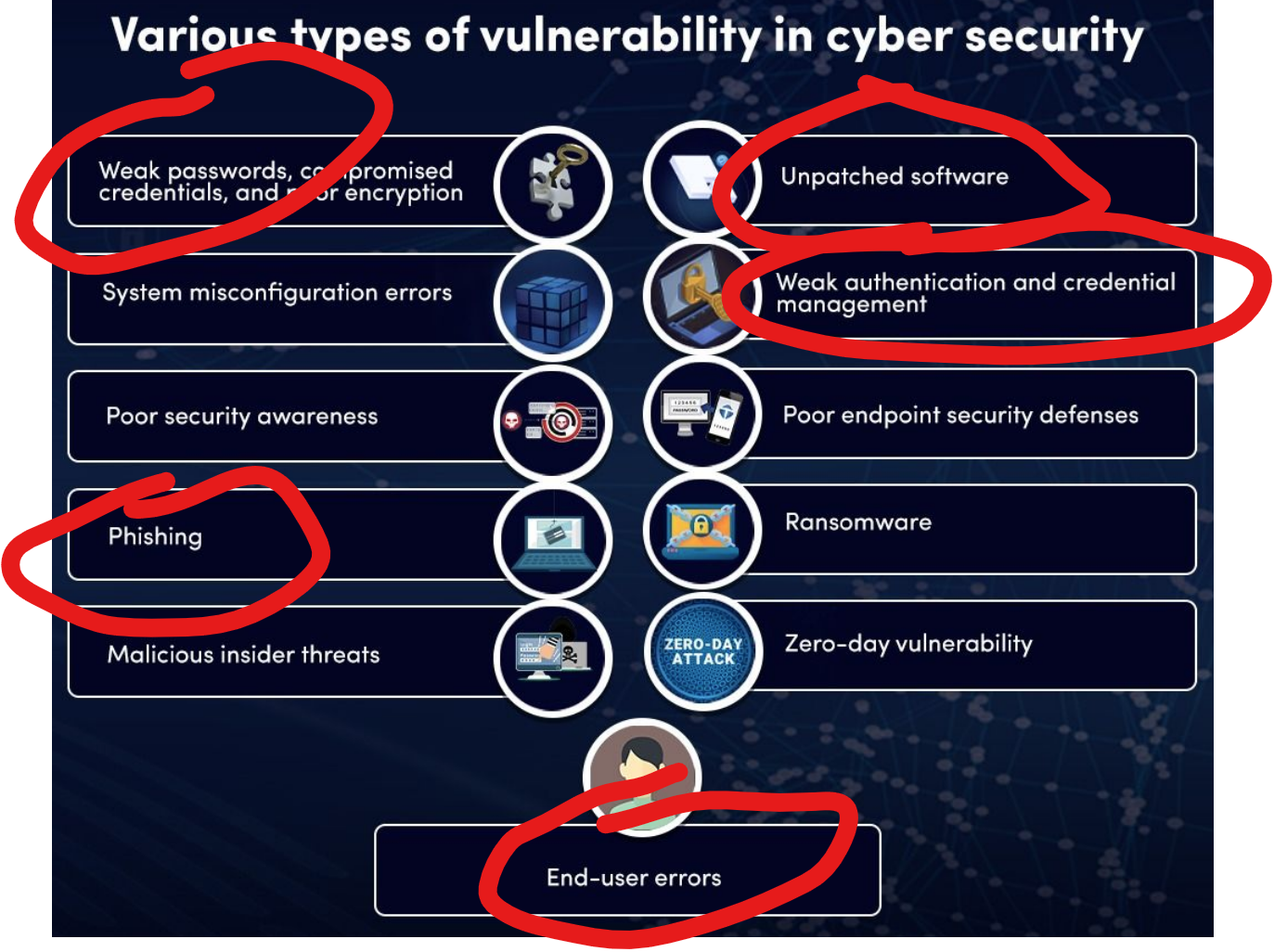
A cybersecurity vulnerability is a weakness within a company’s information systems processes that can be exploited by cybercriminals. Examples of this are using weak passwords, not creating anti-phishing best practices, not maintaining software updates / patches, careless credential management, and using easy-to-guess passwords.
Very rarely are cyber vulnerabilities created as a result of actions taken by cybercriminals, instead, they are usually caused by operating system flaws, network misconfigurations, or end-user errors.
Today’s topic is Password Vulnerabilities. A common tactic cybercriminals employ is to brute force their way into a network by guessing end-user credentials. It is important to understand best practices so that login information cannot be easily exploited to gain access to a computer or network.
- It’s a good approach to make your passwords at least 12-14 characters long.
- Using uppercase and lowercase letters is a must.
- Special characters and numbers definitely add complexity and make it more challenging for hackers.
- Enable Two-Factor authentication whenever possible. While a great passphrase will help secure you, a second factor makes it that much more difficult for hackers to gain access.
- Do not reuse passwords across systems.
- Avoid passwords with patterns such as 12345, QWERTY or ABCDE.
- Avoid using personal information in your passwords such as your name, address, or birthday.
- Never share your passwords with anyone.
- If you no longer need an account, remember to close, disable or delete it.
Although implementing these strategies will make your password-life more difficult, you’ll be glad you did.
Feel free to use Microsoft Authenticator or Google Authenticator to help you create, save, and remember your passwords. FYI, I use both.
the artist for this graphic is unknown. please reach out if you know the creator.



