Phishing vulnerability in cybersecurity
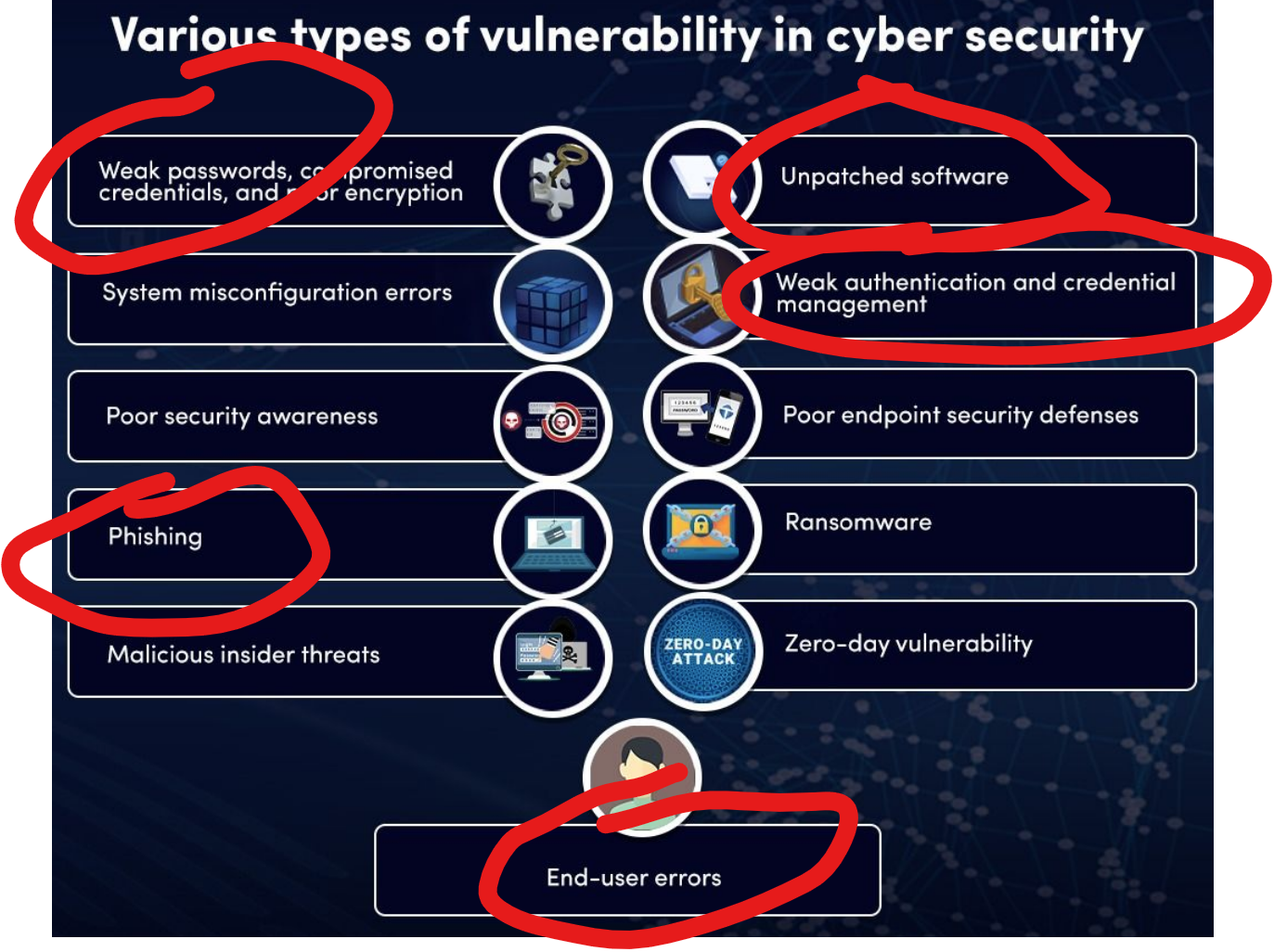
A cybersecurity vulnerability is a weakness within a company’s information systems processes that can be exploited by cybercriminals. Examples of this are using weak passwords, not creating anti-phishing best practices, not maintaining software updates / patches, careless credential management, and using easy-to-guess passwords.
Very rarely are cyber vulnerabilities created as a result of actions taken by cybercriminals, instead, they are usually caused by operating system flaws, network misconfigurations, or end-user errors.
Today’s topic is Phishing. Phishing attacks come from scammers disguised as trustworthy sources and can facilitate access to all types of sensitive data. As technologies evolve, so do cyberattacks. Let’s talk about a couple of the most pervasive types of phishing.
Email phishing. The most common form of phishing, this type of attack uses tactics like phony hyperlinks to lure email recipients into sharing their personal information. Attackers often masquerade as a large account provider like Microsoft or Google, or even a coworker.
Smishing. A combination of the words “SMS” and “phishing,” smishing involves sending text messages disguised as trustworthy communications from businesses like Amazon or FedEx. People are particularly vulnerable to SMS scams, as text messages are delivered in plain text and come across as more personal.
the artist for this graphic is unknown. please reach out if you know the creator.